
Enterprise IT environments are complex, historically grown, and full of exposure — most organizations know something is wrong, but lack the internal capacity to find it, prioritize it, and fix it properly.
ROSTECH is an IT security consultancy based in Innsbruck, Austria. We specialize in three areas where we see the most critical gaps: identity and privileged access, host-based network segmentation, and vulnerability management. We work alongside your IT team — not instead of it — to assess your environment, define what matters most, and implement solutions that hold up in the real world.
For a select number of specialized security platforms in the areas of privileged access management, zero trust segmentation, and secure remote access, we go beyond consulting: we are an authorized reseller and implementation partner. That means a single point of contact from product selection through deployment and ongoing support — no handoffs, no gaps.
We address the most critical security gaps in enterprise IT environments — how identity and access are controlled, how the network is segmented, and how vulnerabilities are identified and resolved. Our work is built around three core disciplines:
VULNERABILITY MANAGEMENT
IDENTITY & ACCESS MANAGEMENT
ZERO TRUST SEGMENTATION
VULNERABILITY MANAGEMENT
IDENTITY & ACCESS MANAGEMENT
ZERO TRUST SEGMENTATION
Getting a complete picture of your exposure requires two distinct approaches — each finding what the other misses. Our self-developed auditing framework Resonate supports assessment, remediation tracking, ongoing validation and vulnerability management in one place.
MANUAL SECURITY ASSESSMENT
We examine your environment for issues that automated tools cannot detect: architectural weaknesses, configuration errors that open unintended attack vectors, credentials exposed in deployment scripts or OSD sequences, and privilege escalation paths buried in years of accumulated access control decisions. This is investigative work — we look at how your environment actually behaves, not just how it is documented.
AUTOMATED VULNERABILITY SCANNING
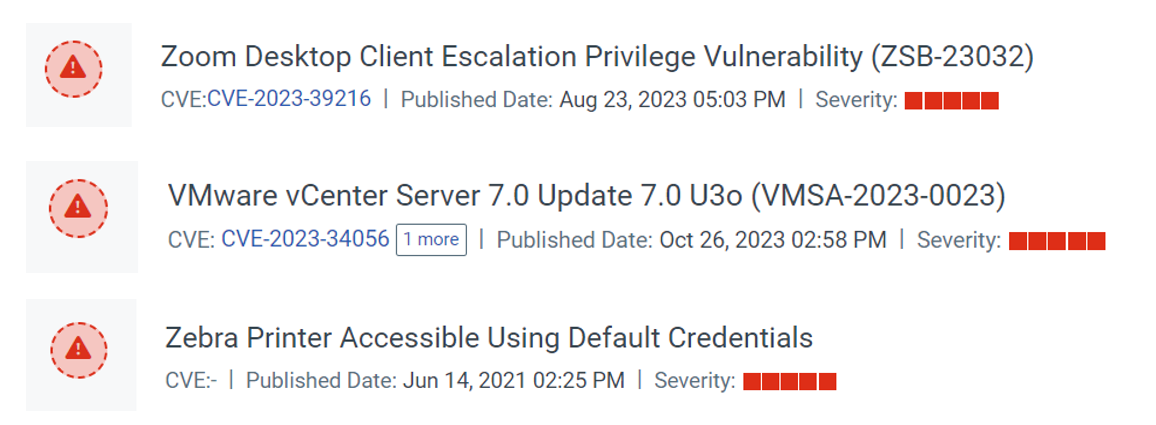
Systematic scanning across internal, external, and agent-based targets surfaces known CVEs and configuration weaknesses at scale. We prioritize findings by actual exploitability and business impact — not raw CVSS scores — and translate results into remediation plans your team can act on. Ongoing scanning cycles create a measurable record of improvement over time.
PRIVILEGED ACCESS MANAGEMENT
Admin credentials are among the highest-value targets in any environment. PAM solutions centralize privileged accounts in a secure vault — with automated credential rotation, session proxying, and full audit trails. Every privileged session is brokered, recorded, and traceable. Endpoint privilege management (EPM) extends this to workstations, enabling least-privilege enforcement without breaking legacy applications.
SECURE REMOTE ACCESS
Traditional VPN grants broad network access — the opposite of least-privilege. We design and implement granular, MFA-enforced remote access solutions that control exactly which systems and protocols (RDP, SSH, web applications) a user or vendor can reach, with full session recording. This is particularly critical for external service providers, where uncontrolled remote access is a frequent attack vector.
MICROSOFT ADMIN TIERING & IDENTITY PROTECTION
We design and implement structured admin tiering — isolating domain controllers and tier-0 infrastructure from regular operational admin activity. This includes privileged administration workstations (PAW), hardening mechanisms, legacy authentication protocol cleanup and admin access enforcement across tiers. The goal: even a fully compromised end user workstation cannot reach your most critical assets.
Perimeter firewalls are necessary — but insufficient. Once an attacker is inside your network, traditional segmentation does little to contain them. Host-based firewalling and zero trust segmentation (ZTS) change that equation fundamentally: every host is isolated by default, and communicates only on explicitly permitted ports from defined sources.
A central processing engine takes system information and uses a label-based abstraction layer to transform policy into actual firewall rules. Independently of networking topology the rules then automatically adjust as your environment changes. This approach makes ZTS far easier to maintain at scale, and dramatically reduces the attack surface for lateral movement, insider threats, and unpatched system exposure.
An advanced traffic visualization layer maps thousands of flows across your environment — grouped by application, location, or custom label — giving you visibility into traffic patterns that never traverse a network firewall and would otherwise be completely invisible.
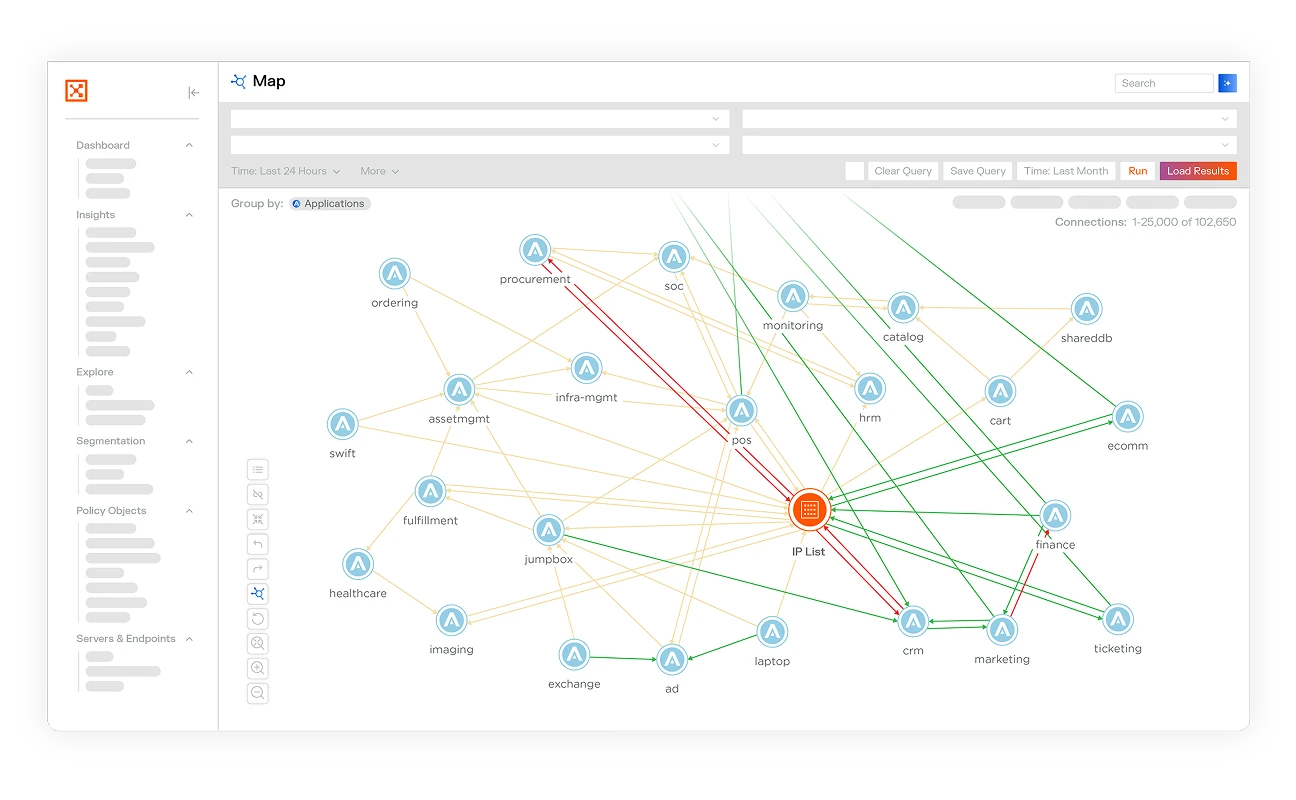
ROS\\TECH has partnered with zero trust segmentation company Illumio to deliver one of the most advanced software-defined host firewalling solutions available. We are certified specialists for Illumio Core SaaS and On-Premise.

In autumn 2025, we delivered a 3-day in-house security workshop at a customer's production facility in the DACH region. Nearly 30 participants from across the organization covered identity protection, network segmentation, vulnerability analysis, and real-world breach scenarios — from how attacks unfold to how they get stopped.

In summer 2025, we were featured in a customer success story published by Illumio. You can find the full story here:
illumio.com/customers/how-swacrit-secures-its-manufacturing-and-simplifies-it-operations-with-illumio